Download Safe download
5 downloads (last 7 days)
Allows users to access computers remotely via a secure connection
Review by Karen M.
Pros
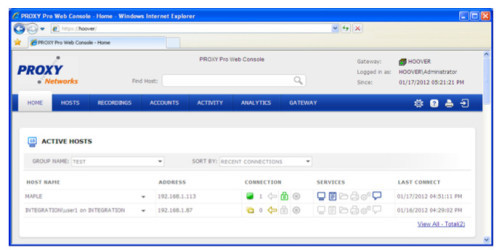
Web-based remote control
The new version of Proxy Network's remote access software, Pro 8.10, allows users to access computers remotely via a secure connection. Clients don't have to worry about unpredictable connections and assistance anymore. When using this remote access software, a properly authorized professional is given access to your device to fix any problems that might arise along the way.
The new version of the software comes with the always-on service, which means computers can be also accessed while they are unattended. If they don't want to be disturbed, clients are no longer required to stand by their devices in order to grant professionals permission to access them.
Additionally, Pro-8 can be used to control a plethora of computers easily. The software comes with a brand new connection management system, which allows for the creation of a centralized directory of machines.
Furthermore, Centralized Authorization methods have been improved. Through these methods, the software allows clients to set fine-grained permissions for control over a group of machines, give chosen users different levels of authorization, and restrict access to remote machines if necessary. It also empowers clients to enable stealth mode access for remote machines by turning off notifications.
Moreover, Proxy's new software comes with additional features, including state-of-the-art encryption algorithms and key strength, which can easily be managed under a centralized audit log for easy, web-based monitoring and access. By using Pro-8, clients can ensure the safety and security of their computers through a trusted software provider.
The new version of the software comes with the always-on service, which means computers can be also accessed while they are unattended. If they don't want to be disturbed, clients are no longer required to stand by their devices in order to grant professionals permission to access them.
Additionally, Pro-8 can be used to control a plethora of computers easily. The software comes with a brand new connection management system, which allows for the creation of a centralized directory of machines.
Furthermore, Centralized Authorization methods have been improved. Through these methods, the software allows clients to set fine-grained permissions for control over a group of machines, give chosen users different levels of authorization, and restrict access to remote machines if necessary. It also empowers clients to enable stealth mode access for remote machines by turning off notifications.
Moreover, Proxy's new software comes with additional features, including state-of-the-art encryption algorithms and key strength, which can easily be managed under a centralized audit log for easy, web-based monitoring and access. By using Pro-8, clients can ensure the safety and security of their computers through a trusted software provider.
Additional details
Latest version
8.10
Language
English | German
Total Downloads
3,772
Works with
Windows 2000, XP, 2003, Vista, 7, 2008, 8, 8.1
Date
9 years and 6 months ago
Developer
Proxy Networks, Inc.Security analysis
Trusted
Alternatives to Proxy Pro Remote Desktop Software
Access to remote computers or share your own with this portable version of TeamViewer